Real World Assets on Blockchain: Tokenisation, Mechanics and the Regulatory Frontier
Understand exactly how RWA tokenisation works — the legal wrappers, oracle dependencies, and risk layers most guides skip. Move from surface-level awa…
Ready to go deeper? Explore DeFi protocols, staking strategies, cross-chain bridges, Layer 2 solutions, and more.

Understand exactly how RWA tokenisation works — the legal wrappers, oracle dependencies, and risk layers most guides skip. Move from surface-level awa…
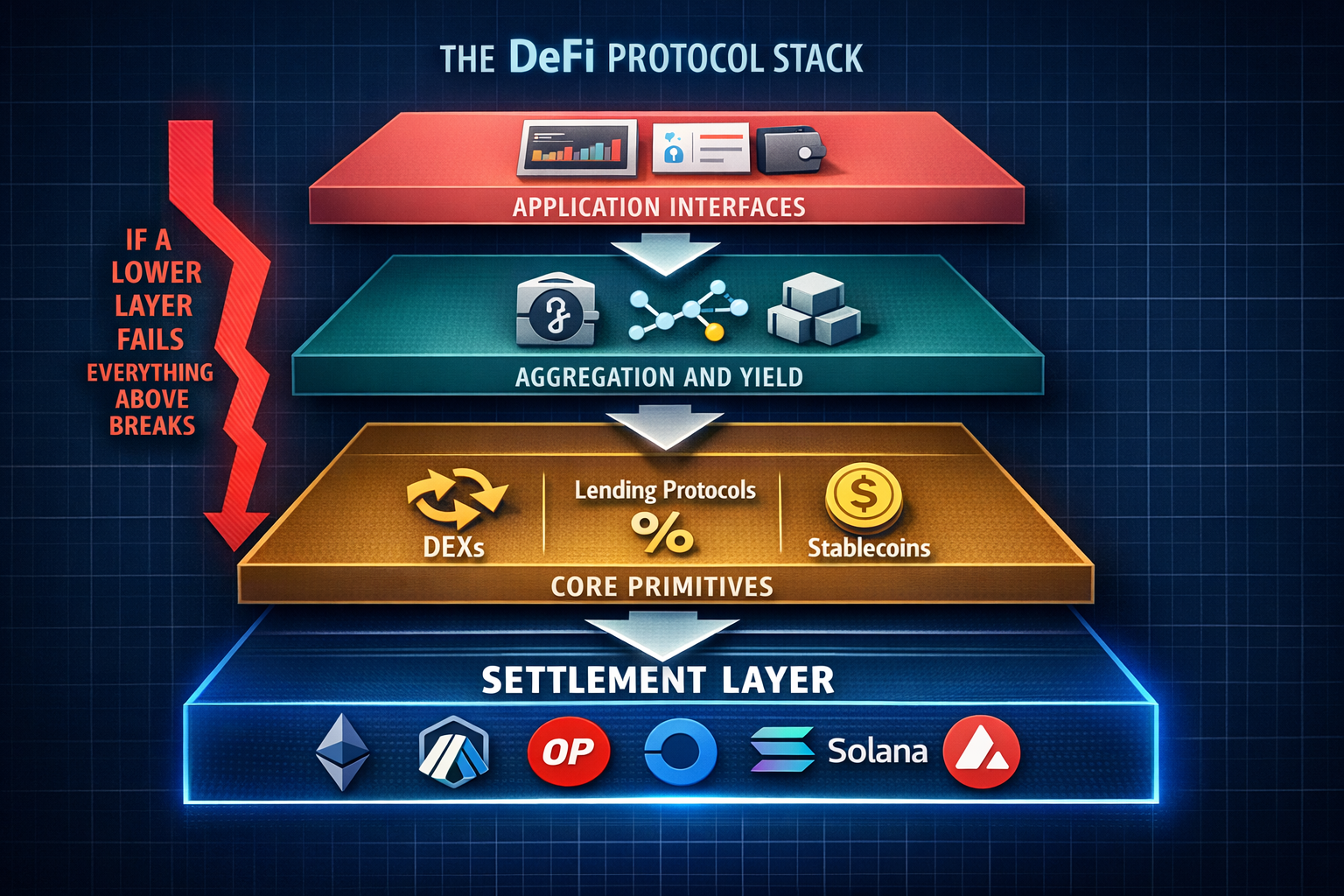
Understand the actual mechanics behind every DeFi primitive — swaps, lending, staking, bridges — and the specific risks compounding across each layer.…
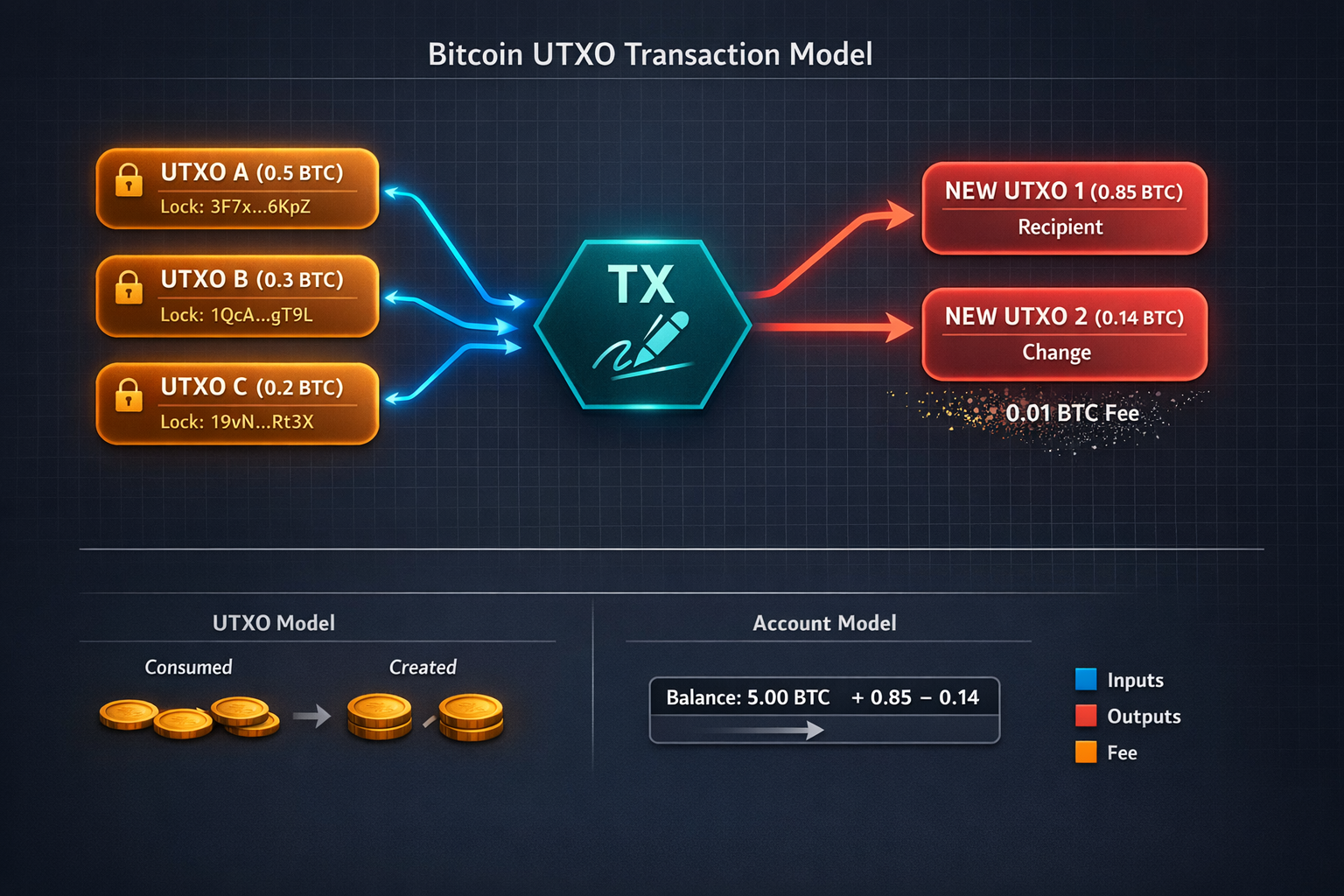
Master Bitcoin's protocol mechanics, post-halving economics, Lightning scaling, and institutional infrastructure. After reading, you'll understand the…

Maps the real Web3 job ecosystem in 2025 — which roles exist, how compensation works on-chain, and where hiring is concentrating. Cuts through LinkedI…

ENS, Handshake, and Unstoppable Domains created new naming systems. Doma tokenizes real internet domains (.com, .ai, .xyz) as programmable assets on a…

Explains the cryptographic mechanics behind STARK proofs and how StarkNet uses them to batch thousands of transactions into a single Ethereum proof. C…

What actually happens when you run an Ethereum validator — the two-client architecture, real hardware specs, and slashing risks most guides gloss over…

The IRS requires crypto reporting in more situations than most holders realize, and fewer than panic suggests. This guide covers the actual rules, for…

DAOs without legal wrappers expose every token holder to unlimited personal liability. This guide covers the real mechanics of LLC wrappers, UNA struc…

Most bridge comparisons stop at 'trusted vs. trustless.' This guide breaks down the actual verification mechanisms, validator economics, and failure m…

Maps the real regulatory frameworks governing tokenized real-world assets across key jurisdictions in 2025. Covers what's enforceable now, what's in t…

A concrete checklist for evaluating DeFi protocol risk before depositing funds. Covers smart contract exposure, token approvals, liquidity depth, and…